What breaks passwords isn’t human error. Speed does. Work unfolds quickly now. Access must be ready when someone starts Monday morning. Outside partners require entry for short spans. Departments adopt cloud apps silently. Yet a single repeated credential or an account with excessive rights is enough for intruders to slip through. That is why identity and access management matters. Who gets in, when they do it, and how – that stays clear because of structured oversight. Work keeps moving smoothly, even as boundaries remain firm through automated checks rather than endless sign-offs.
What Identity and Access Management Really Means
Gartner sees IAM not just as tools, but as structured practices guiding who – whether person or system – gets access, when they need it, why they require it. Access arrives only under valid conditions; improper attempts meet immediate denial. Security stays central, yet flexibility supports real-world demands. Unauthorized entry points vanish through design.
In essence, identity management handles access control by defining who can do what within a system
- User accounts and logins across apps and devices
- Permissions and roles, especially admin access
- Verification power depends on methods such as multi-factor authentication, while newer logins resist deceptive attacks through stronger safeguards
- Access for vendors, contractors, and temporary staff
- Regular check-ins keep entry rights from stacking up unnoticed
Why IAM is Now The Center of Business Security
The old security model assumed your “network” was the boundary. Now the boundary is identity. When someone signs in to email, CRM, file storage, or cloud dashboards, that sign in becomes the new front door.
That is also why federal and industry frameworks push hard on stronger identity proofing and authentication. NIST’s Digital Identity Guidelines lay out structured approaches for identity proofing, authentication, and federation, and the guidance has been updated into the newer SP 800-63-4 suite as of August 2025.
The IAM Breakdowns We See Most Often
Folks who know their stuff still stumble on familiar hurdles. What seems obvious often hides repeating traps beneath. Patterns repeat, despite skill levels involved. Trouble shows up quietly, even among sharp groups. Experience does not block recurring missteps. Familiar loops catch attention only after problems arise
Access sprawl
Access often remains even when job duties shift. With time, group email boxes tend to stay active. Former contractors sometimes retain entry points.
Too many admins
One overlooked login escalates when access multiplies unchecked. A single breach shifts small oversight into full disruption – speed trades safety, quietly.
MFA gaps that attackers hunt for
A single outdated application, a lone “temporary” bypass, or even one high-profile user rejecting multi-factor authentication might erase extensive security progress. According to CISA, the path forward is straightforward – enforce MFA, particularly when handling off-site logins or elevated permissions.
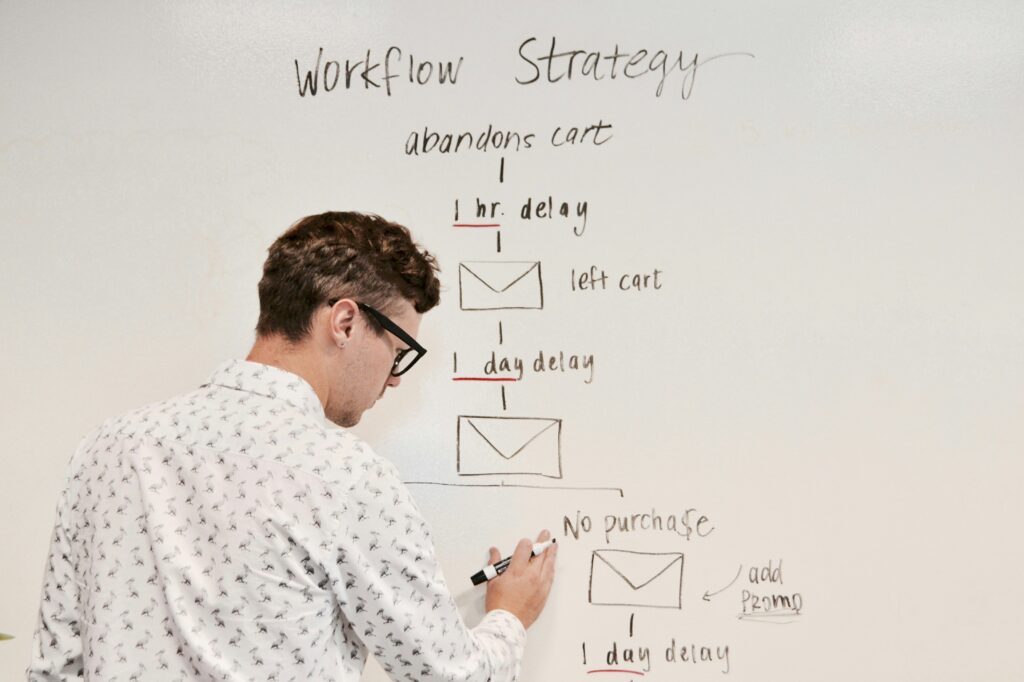
No conditional access strategy
Access must respond to signs of risk, yet rely on more than passwords alone. One way firms manage this: Microsoft Entra Conditional Access applies policies shaped by live threat indicators instead of static credentials.
The 5 Pillars of Strong IAM
1. Central Identity Directory
One way to begin is bringing identity management together, stopping each application from acting independently. Where feasible, move in the direction of single sign-on – this simplifies how access works, also making removal smoother when needed.
2. Least Privelege, Enforced by Roles
Then tighten permissions so users only get what they need. Role based access makes onboarding faster, and it also keeps people from accumulating random permissions over time.
3. MFA Everywhere, With Stronger Methods for High Risk Accounts
Defaulting to MFA makes more sense than treating it as an add-on. Following this, stronger safeguards for high-access accounts matter – especially through anti-phishing tools when available. Because common login breaches often fail under MFA, CISA highlights it as essential security groundwork.
4. Conditional Access and Device Trust
Later on, include guidelines about timing along with methods. An illustration might be:
- Block sign ins from impossible travel patterns
- Require compliant devices for sensitive apps
- Require tougher verification when administrators perform critical tasks
Flexibility in policy enforcement comes through conditional access, yet full oversight stays intact. While rules adapt as needed, authority remains firmly held.
Ongoing Access Reviews and Lifecycle Cleanup
Finally, build a repeatable habit of reviewing access. If you only clean permissions during offboarding, you will miss the quieter risk: users who stay employed but change roles.
A Realistic Rollout Plan That Does Not Break Productivity
If you want IAM that sticks, sequence matters:
- Inventory identities and apps (employees, contractors, vendors, shared accounts)
- Fix the worst MFA gaps first (admins, remote access, email)
- Standardize roles and permissions for core apps
- Turn on conditional access for high value systems
- Implement access reviews on a set cadence
- Harden privileged access with separate admin accounts and stronger controls
This approach reduces risk quickly, and it keeps your team from getting overwhelmed. If you already have internal IT, co-managed IT services help you roll this out faster without losing control.
-
1) What is identity and access management, in simple terms?
Identity and access management is how a business controls who can sign in, what they can reach, and what they can change across systems. It combines logins, permissions, MFA, and ongoing access reviews so access stays organized as teams grow.
-
2) Is MFA enough on its own?
No. MFA helps a lot, but it doesn’t fix excess admin rights, stale accounts, vendor access that never expires, or risky sign-ins from unknown devices. Strong IAM adds role-based access, conditional access rules, and routine cleanup so MFA isn’t your only safety net.
-
3) When should a business invest in IAM improvements?3) When should a business invest in IAM improvements?
If you use multiple cloud apps, onboard staff often, rely on vendors, or have more than a few admins, you’re already in IAM territory. Most companies should improve IAM before a security audit, insurance renewal, migration, or rapid hiring push—because those moments expose gaps fast.
How Titan Elite Supports Identity and Access Management in Los Angeles
Most LA companies struggle with IAM – not because of complexity, but due to split responsibilities. Devices fall under IT’s control. Security manages the software layer. Access permissions come from department leads. Onboarding sits with HR instead. Without a single leader guiding the full process, pieces slip through each transfer. That’s where vCIO services help, one owner for decisions, priorities and accountability.
Titan Elite fills these openings through a hands-on approach. A system that works follows clear steps without confusion. Instead of theory, it relies on real tasks getting done. Each part connects logically, avoiding loose ends. Structure comes from consistent practice rather than complex rules. Gaps disappear when actions align smoothly
- A clear IAM baseline for your core apps and cloud logins
- MFA and conditional access policies that match your risk profile
- Role and permission cleanup that stays aligned to real job functions
- Via strict permissions, vendor logins expire automatically. Temporary credentials replace permanent ones. Access ends when tasks finish. Systems enforce time-limited entry by design. Privileges reset after use. No account remains active indefinitely
- As growth happens, access remains tightly controlled through continuous evaluation
Focused on easing entry for new users, the process reduces exceptions significantly. Because of this, unauthorized account access drops. When leaders question current permissions, answers come clearly. Access details stay updated, so oversight feels less tangled. Simpler checks mean fewer surprises later.


